Experts have revealed just how easy it is for people to hack your password.
Many of us perhaps think the foolproof 'password' or '123456' is enough to bypass the mischievous internet nerds.
Well, it turns out, passwords even more complex than the ones above are also pretty easy to break in to.
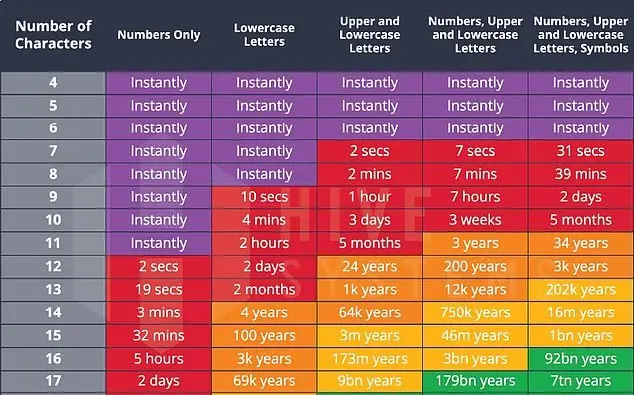
According to new research, any variation of a six figure password can be cracked instantly.
Advert
Even an eight figure character combo can be guessed in roughly 39 minutes, according to cybersecurity company Hive Systems in Richmond, Virginia.

Although, if you want to be super safe, an 18 character password won't be cracked for around 438 trillion years - as long as it includes some numbers, symbols and a mix of upper and lowercase characters of course.
I mean, unless you want to be writing an essay every time you log in, it turns out that a strong 11 character password would be cracked within some 34 years, which seems like a happy medium.
The company said its data was 'based on how long it would take a consumer-budget hacker to crack your password hash using a desktop computer with a top-tier graphics card'.
"If you use the same password on multiple sites, you're in for a bad time," Hive Systems wrote.
The company also discussed 'hashing', which is a term referring to a scrambled version of text that sort of reconfigures it.
Basically, if the word 'password' is hashed, the output would be 5f4dcc3b5aa765d61d8327deb882cf99.
Long story short, passwords saved on websites, are stored in servers as hashes, as opposed to plain text passwords.
The hash is impossible to reverse so all hackers will see is the jumbled up reconfiguration.
However, hackers will then make a list of all of the characters on your keyboard and then that's where the hashing begins.
They will then compare their list of hashes with the stolen password and then they're able to figure out your login.
Seems like a lot of work, but it's definitely not uncommon.
"We reviewed password data breaches from 2007 to present, reported through HaveIBeenPwned, to see what attackers have actually been trying to crack and whether that changed over time," Hive Systems said.
"Generally speaking, website logins that people probably care less about, like forums and restaurants, used and continue to use MD5 and SHA-1.
"That is a pretty big deal assuming people reuse the same passwords on more concerning sites like banking, government, private messaging, email, and social media."
Topics: Technology