News
The latest national and international news stories that will inform you, make you laugh and make you think.
The latest national and international news stories that will inform you, make you laugh and make you think.
The latest national and international news stories that will inform you, make you laugh and make you think.

Gemma Monk had her 2024 wedding ruined by sister-in-law Antonia Eastwood

Tiana Krasniqi watched death row inmate James Broadnax take his last breaths just over two weeks after they tied the knot
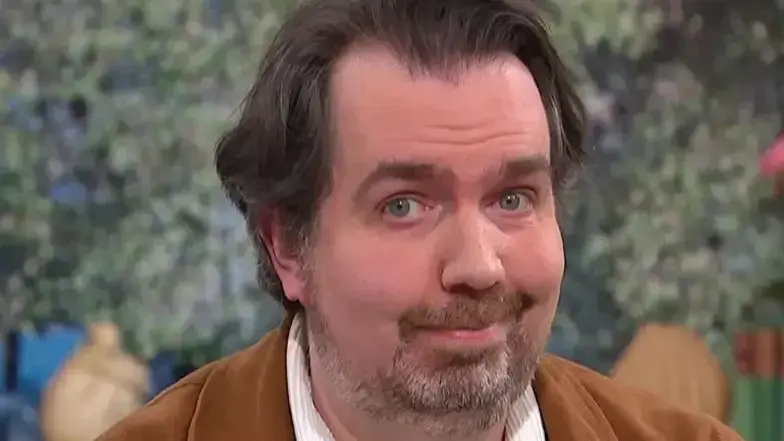
It's not always a blessing for Barr

He'd quit vaping before and wanted to 'quit it for good'